Lookalike domain threats, automated takedowns, certificate tracking.
- 24/7 Monitoring
- Lookalike Domains
- New Domains
- Subdomain Takeover
- Rapid Takedowns
- Weekly Reports
- Platform Access
- Certificate Tracking
Core domain monitoring for lookalike threats, automated takedowns, and certificate tracking.
Lookalike domain threats, automated takedowns, certificate tracking.
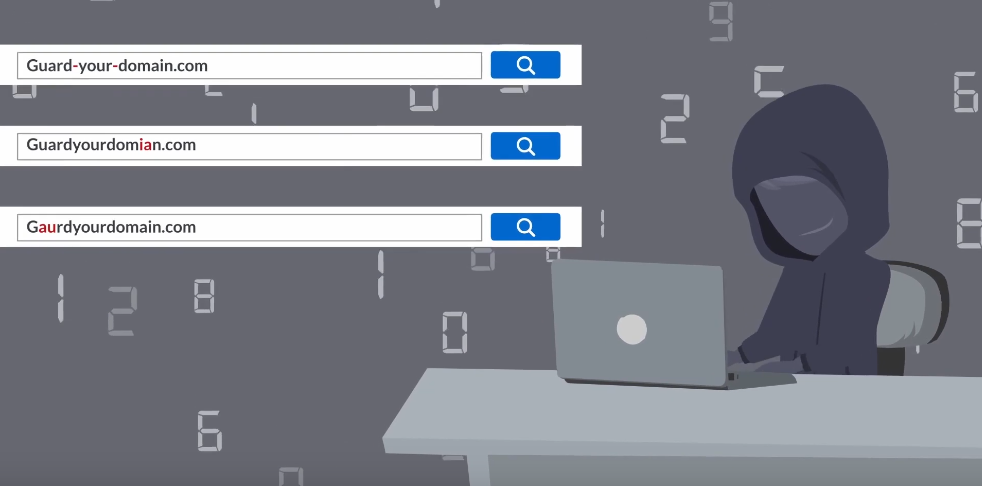
Domain Monitoring is the process of scanning public domain data sources, in order to identify similar looking domains.
Assuming a domain is available, anyone can register a look-alike domain targeting any institution with ease. Some individuals go as far as to track expiring domains in order to scoop up the newly expired domains as soon as they become available.
DomainGuard scans and ingests data from various public and private data sources to identify lookalike domains.
Lookalike domains are used by attackers to target your employees or your customers. Employees are tricked into entering fake company portals using their company credentials while customers are tricked into submitting personal financial information when visiting a site such as a fake banking site or a fake online retail store.
By tracking lookalike domains from their inception, DomainGuard takes a proactive approach to phishing and fraud prevention. DomainGuard regularly identifies phishing sites and infrastructure before the cyber-criminals have begun their attack.

Continuous data harvesting and analysis algorithms pinpoint real threats to your domain, reducing the time wasted on chasing down non-threats.
While our technology does the heavy-lifting deep analysis, we will always use human intelligence for final analysis and determination of threats to your organization.
Help defend your organization and customers from cyber criminals and making the internet a safer place to conduct business.
It starts with 24/7 continuous monitoring and ends with an automatic takedown. Your team can sit back and relax while we manage the takedown workflow.
DomainGuard scans the internet for domains and other artifacts similar to your company's domain and brand.
DomainGuard categorizes approved assets and separates them from potential threats.
DomainGuard monitors artifacts until malicious intent is identified.
DomainGuard automatically issues a takedown request when malicious intent is identified.

From malicious-intent detection to takedown request, measured in seconds, not days.